Our team has an extensive expertise in the field of Internet Security from the 1980's through present day. We have worked with government agencies, private sector, corporate business, non-profits, utility companies, and interviewed by National Security Magazine.
Today your network is more than sharing files and printers in the office; it requires the seamless integration of local-area-networks with wireless-local-area-networks, and accessibility via a wide-area-network with cloud architecture. Our collegiate system generates thousands of graduates annually with degrees in networking; however, it requires a seasoned experienced network technician to synchronize the variety of every changing protocols.

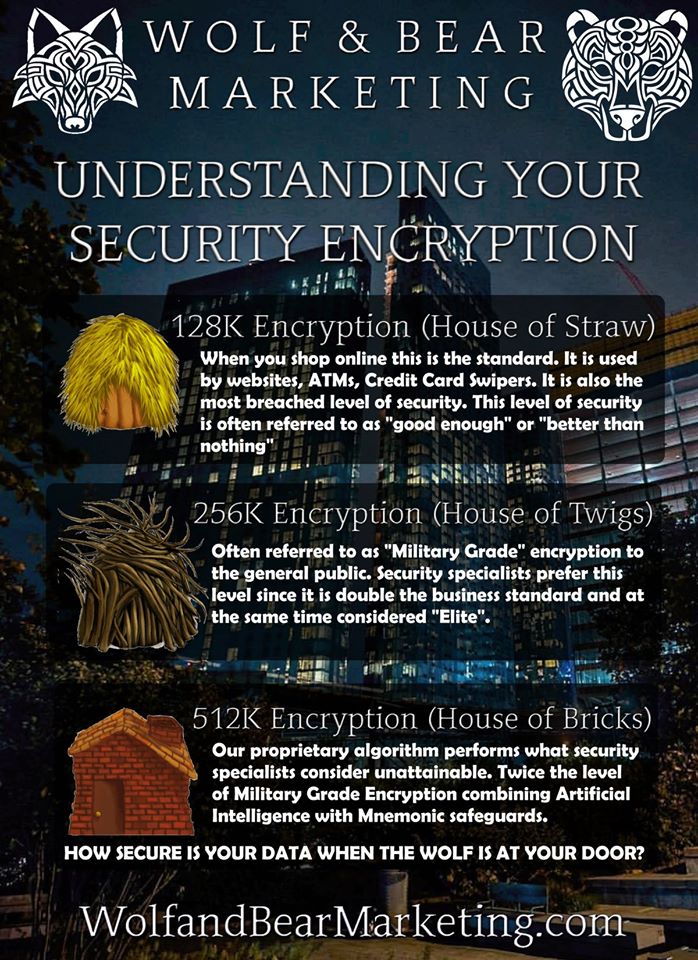
In order for hardware and software security measures to be effective, small businesses must incorporate computer security into their basic operations. We recommend that small business owners establish a set of policies and procedures for Internet security. These policies should encompass computer activity at both the user level and the system administrator level.
In order to prevent unauthorized external access to the computer system, administrators should define access rights granted to suppliers and customers. They should also make sure Internet ports are secure, and possibly implement a firewall to protect the internal network from outside access. Another important policy is never to store employee passwords on any computer that is connected to the Internet. Administrators should also be careful about establishing guest accounts on the company's computer system, since some such requests may come from hackers or competitive spies.